Passwords have long been one of the central pillars of account security on the Internet. Combined with a username, they make up the foundation of most login systems. Because of this, they are a hot commodity for hackers who want to steal credentials and infiltrate accounts or networks. In recent years, however, other security measures have exposed the weakness of poor passwords for security, leading to the adoption of other measures.
EZ MSP Blog
Obviously, we won’t tell you to cut down on your cybersecurity. That said, it can be easy to overinvest and overreach if you aren’t careful about what you’re implementing. This phenomenon is known as cybersecurity sprawl, and if not prevented, it can easily have serious consequences for your business. Let’s go into how to avoid this sprawl.
When you think of a scammer, you probably think of someone looking to take advantage of someone for their own gain. While this isn’t wholly inaccurate, another variety exists to acknowledge… those who aim to scam the scammers. Let’s consider one such white-hat scammer, or “scam baiter,” a content creator who uses the alias “Kitboga,” Kit for short.
Unfortunately, cyberattacks will only continue in the weeks, months, and years to come, making it increasingly essential that businesses have access to cybersecurity expertise. Even more unfortunately, professionals with this level of expertise are becoming harder to find. Globally, we’re short almost four million people, and those we have are prone to make mistakes in their first few years. This comes from a report by Kaspersky, entitled “The Portrait of Modern Information Security Professional,” Let’s review what the cybersecurity developer found and what we can take away from these findings.
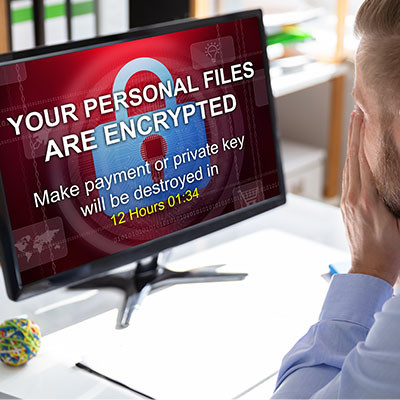
We’ve spent the last few weeks discussing ransomware's impacts on different subsets. First, we discussed how a ransomware attack impacts the customers of the infected business, and then we touched on the infected business itself. To end, we want to touch on ransomware's impacts on society, specifically regarding economic health and geopolitical security, known as third-order harms.
Have you ever heard of the “man-in-the-middle” attack or MitM? It’s a situation where your data is stolen by an onlooker who situates themselves in the right place at the right time. Data interception is a very real thing that your business should be prepared to fight against. Let’s discuss some strategies you can use to counter these sneaky attacks.
It can be too easy to look at ransomware as a business problem. After all, it attacks businesses, locking down their data for ransom, often selling it or spreading it, and sometimes altering it for the business if returning it at all. It can be too easy to overlook another impacted target in all the mess.
What happens to the people whose data a business has collected and uses?
There are many parts of running a business where you cannot be too careful, one of which is the realm of cybersecurity. Many of the preventative measures you can implement aim to keep issues from making their way to your infrastructure in the first place, which makes sense from an operational standpoint. With an endpoint detection and response solution—or EDR—you’ll take an important step toward keeping most threats off your infrastructure.
On Wednesday, April 10, 2024, Apple deemed it necessary to send a rare alert to certain users via email, spread out across 92 nations. As Apple’s website states, these threat notifications “are designed to inform and assist users who may have been individually targeted by mercenary spyware attacks.” Let’s review these attacks so we all understand this threat better.
Your typical IT professional might suggest some common methods of network security like implementing better preventative measures, like firewalls and antivirus. However, there is more that goes into network security—far more. If you’re not careful, you could accidentally miss some of these three security solutions and expose your business to potential threats. But we’re not about to let that happen!
Mobile malware isn’t common, but it’s growing increasingly more so. You may have heard of a malware called XLoader, which has been used to victimize people in over seven countries. This mobile threat has seen various iterations over the past several years, but you should be especially concerned these days.
For the IT administrator and the small business owner, it can be a bewildering experience when your company comes under siege from employee-induced cyberthreats; especially if you, like many other companies, have started prioritizing security training. Even if the threat is thwarted early and the effect on the business is negligible, it is important that you trust the people who have access to your organization’s digital resources. Let’s look at some of the reasons some of your staff take cybersecurity initiatives worse than others.
The constant fear of falling victim to scams has become a harsh reality and is far from ideal. However, the good news is that there is always time to acquire the skills needed to avoid such scams. Let's explore ways to enhance awareness regarding the challenges posed by scams, not only in a business context but also in everyday life.
If you are old enough to remember when antivirus (like most computer software) came in a great big textbook-sized box at the store, then you probably remember a time when that was the only protection you really needed.
Today, there are countless free versions of antivirus out there. Let’s talk about how much protection these actually bring, and when and where they might be a good fit.
We’re hoping that you are actually reading this post to prepare yourself if your business were to face a ransomware attack, but if you are suffering from one right now, we encourage you to reach out to us immediately, whether you are a client or not. Ransomware spreads quickly, and once it has infected a system, there really isn’t much you can do to stop it. However, there are steps you need to take to come back from this gracefully.
Unsurprisingly, some of the biggest retail days of the year are some of the biggest days for scams, the entire holiday season seeing an increase in threats toward retailers and, as a result, the consumers that are just looking for that perfect gift for their loved ones. Let’s review some statistics and trends to see what insights we can glean.