Social media is constantly evolving, and if the big social networks had it their way, it would be the only place people go when they log onto the Internet. Whether you have strong feelings for or against social media, or perhaps you are indifferent, it’s important to understand how to protect yourself when using social media.
EZ MSP Blog
Have you ever seen the file types that look like normal folders, but they have a zipper on the icon? These are ZIP files, and they are helpful for a variety of reasons. We’re sure you have encountered zipped files throughout your time using technology, and today, we want to demystify them a little bit and show you how to use them effectively.
While AI is far from perfect, I always love discovering ways that it can help do something mundane and speed up a workflow here or there. I’m no expert in Photoshop either, so if I need to edit something, I usually depend on someone with a little more experience, but this was a really neat trick I was able to do in just a few minutes!
Emerging technologies offer significant opportunities for businesses to achieve their goals. However, understanding how and when to leverage these technologies is crucial. One of the most rapidly advancing technologies today is artificial intelligence (AI). Yet, AI encompasses more than what one might initially think. Many of the most impactful business tools are powered by a branch of AI called machine learning (ML). This month's newsletter delves into machine learning, its mechanics, and its applications within a business context.
Passwords have long been one of the central pillars of account security on the Internet. Combined with a username, they make up the foundation of most login systems. Because of this, they are a hot commodity for hackers who want to steal credentials and infiltrate accounts or networks. In recent years, however, other security measures have exposed the weakness of poor passwords for security, leading to the adoption of other measures.
Note taking apps are really useful and Microsoft OneNote is one of the most available and feature rich apps on the market for this use. You are probably familiar with the sticky note. They are notes that give a solid visual representation of items that workers need to be cognizant of for all types of processes. In today’s blog, we will go through the process of creating “sticky notes” in OneNote.
Big data is now a crucial resource for businesses of all sizes, including small enterprises. Today, businesses have unprecedented access to vast amounts of data, enabling them to make more informed decisions and operate more efficiently. This month’s newsletter explores how small businesses harness big data's power.
There will always be times when you have to invite guests and other external users to your Microsoft Teams meetings, especially if you want to take advantage of the many collaboration options offered through the platform. However, you need to be very careful with guests and external users–especially in today’s cybersecurity-centric world.
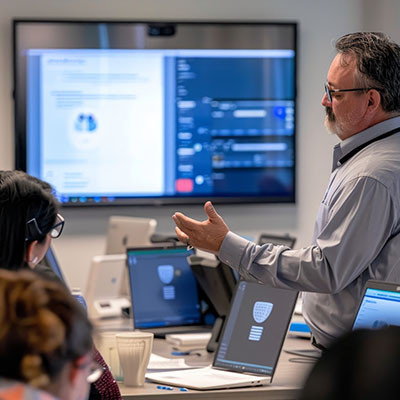
Technology plays a massive role for most organizations nowadays, and not everyone always grasps the importance of it. Most of the time, there is so much built into today’s enterprise software that it can often be overwhelming for workers to use it effectively. Today, we will give you three tips on how to help employees get a grasp of the technology their productivity depends on.
Obviously, we won’t tell you to cut down on your cybersecurity. That said, it can be easy to overinvest and overreach if you aren’t careful about what you’re implementing. This phenomenon is known as cybersecurity sprawl, and if not prevented, it can easily have serious consequences for your business. Let’s go into how to avoid this sprawl.
Technology is a major part of today’s business. It’s fair to say anyone that works in business today is at least semi-proficient with the technology needed to complete their tasks. Unfortunately, for many people, however, the fact that their business requires complicated technology is problematic. This is because at any given moment there are people looking to undermine their job, seeking access to accounts that will allow them to siphon money and data from organizations.
When you think of a scammer, you probably think of someone looking to take advantage of someone for their own gain. While this isn’t wholly inaccurate, another variety exists to acknowledge… those who aim to scam the scammers. Let’s consider one such white-hat scammer, or “scam baiter,” a content creator who uses the alias “Kitboga,” Kit for short.
The world’s largest ticket retailer is in hot water after their parent company, Live Nation Entertainment filed an 8-K filing with the Security and Exchange commission admitting that they had been hacked to the tune of 1.3 terabytes of information. That amounts to 560 million customers’ personal information that has been stolen from the company’s servers. Today, we take a look at the hack and what it means for consumers.
It can be challenging to deal with failure in any context, but in the case of your workplace projects and other efforts, it can be particularly harsh. This makes it all the more important to frame such failures as opportunities to grow in the future.
Let’s discuss six reasons an initiative may fail and the lessons that can be learned from these situations.
Unfortunately, cyberattacks will only continue in the weeks, months, and years to come, making it increasingly essential that businesses have access to cybersecurity expertise. Even more unfortunately, professionals with this level of expertise are becoming harder to find. Globally, we’re short almost four million people, and those we have are prone to make mistakes in their first few years. This comes from a report by Kaspersky, entitled “The Portrait of Modern Information Security Professional,” Let’s review what the cybersecurity developer found and what we can take away from these findings.
We’ve spent the last few weeks discussing ransomware's impacts on different subsets. First, we discussed how a ransomware attack impacts the customers of the infected business, and then we touched on the infected business itself. To end, we want to touch on ransomware's impacts on society, specifically regarding economic health and geopolitical security, known as third-order harms.