Social media is constantly evolving, and if the big social networks had it their way, it would be the only place people go when they log onto the Internet. Whether you have strong feelings for or against social media, or perhaps you are indifferent, it’s important to understand how to protect yourself when using social media.
EZ MSP Blog
Obviously, we won’t tell you to cut down on your cybersecurity. That said, it can be easy to overinvest and overreach if you aren’t careful about what you’re implementing. This phenomenon is known as cybersecurity sprawl, and if not prevented, it can easily have serious consequences for your business. Let’s go into how to avoid this sprawl.
When you think of a scammer, you probably think of someone looking to take advantage of someone for their own gain. While this isn’t wholly inaccurate, another variety exists to acknowledge… those who aim to scam the scammers. Let’s consider one such white-hat scammer, or “scam baiter,” a content creator who uses the alias “Kitboga,” Kit for short.
The world’s largest ticket retailer is in hot water after their parent company, Live Nation Entertainment filed an 8-K filing with the Security and Exchange commission admitting that they had been hacked to the tune of 1.3 terabytes of information. That amounts to 560 million customers’ personal information that has been stolen from the company’s servers. Today, we take a look at the hack and what it means for consumers.
It can be challenging to deal with failure in any context, but in the case of your workplace projects and other efforts, it can be particularly harsh. This makes it all the more important to frame such failures as opportunities to grow in the future.
Let’s discuss six reasons an initiative may fail and the lessons that can be learned from these situations.
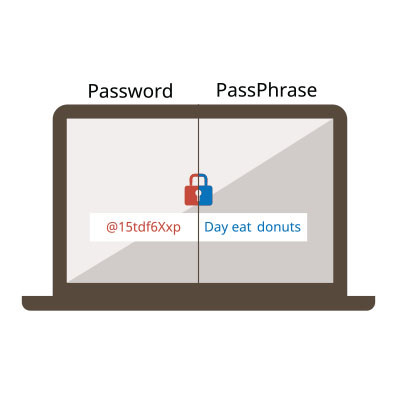
Technology is a major part of today’s business. It’s fair to say anyone that works in business today is at least semi-proficient with the technology needed to complete their tasks. Unfortunately, for many people, however, the fact that their business requires complicated technology is problematic. This is because at any given moment there are people looking to undermine their job, seeking access to accounts that will allow them to siphon money and data from organizations.
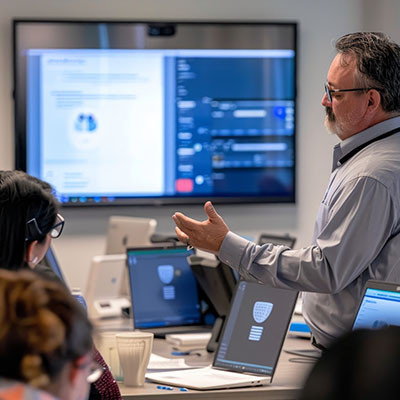
Unfortunately, cyberattacks will only continue in the weeks, months, and years to come, making it increasingly essential that businesses have access to cybersecurity expertise. Even more unfortunately, professionals with this level of expertise are becoming harder to find. Globally, we’re short almost four million people, and those we have are prone to make mistakes in their first few years. This comes from a report by Kaspersky, entitled “The Portrait of Modern Information Security Professional,” Let’s review what the cybersecurity developer found and what we can take away from these findings.
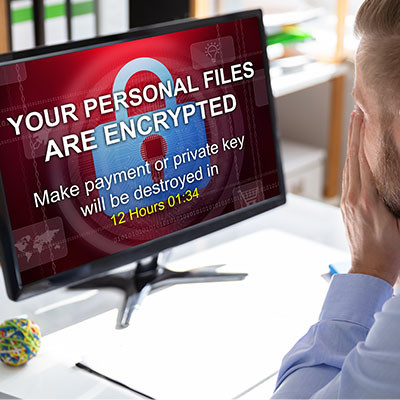
We’ve spent the last few weeks discussing ransomware's impacts on different subsets. First, we discussed how a ransomware attack impacts the customers of the infected business, and then we touched on the infected business itself. To end, we want to touch on ransomware's impacts on society, specifically regarding economic health and geopolitical security, known as third-order harms.
Have you ever heard of the “man-in-the-middle” attack or MitM? It’s a situation where your data is stolen by an onlooker who situates themselves in the right place at the right time. Data interception is a very real thing that your business should be prepared to fight against. Let’s discuss some strategies you can use to counter these sneaky attacks.
It can be too easy to look at ransomware as a business problem. After all, it attacks businesses, locking down their data for ransom, often selling it or spreading it, and sometimes altering it for the business if returning it at all. It can be too easy to overlook another impacted target in all the mess.
What happens to the people whose data a business has collected and uses?
Phishing is one of the most prevalent issues individuals and businesses must confront when operating online. This is because there are literally billions of these scam attempts sent each day. That’s right, billions. With over a hundred billion scam attempts sent every year, your business is already getting phished, it’s just a matter of time before someone falls for it.
There are many parts of running a business where you cannot be too careful, one of which is the realm of cybersecurity. Many of the preventative measures you can implement aim to keep issues from making their way to your infrastructure in the first place, which makes sense from an operational standpoint. With an endpoint detection and response solution—or EDR—you’ll take an important step toward keeping most threats off your infrastructure.
On Wednesday, April 10, 2024, Apple deemed it necessary to send a rare alert to certain users via email, spread out across 92 nations. As Apple’s website states, these threat notifications “are designed to inform and assist users who may have been individually targeted by mercenary spyware attacks.” Let’s review these attacks so we all understand this threat better.
Small businesses are presented with the challenging prospect of monitoring and policing various IT-related policies that you might have for your network infrastructure and workplace technology use. The difficulty of this notion does little to lessen its importance, however. You need to take action to protect your assets, data, and reputation from the countless threats out there, and ensuring that your employees are properly using technology is paramount to this endeavor.